Tech News Blog

Empower Your Business With Reliable IT Support in San Diego
Running a business today means relying on technology more than ever. Your team depends on fast networks, secure systems, reliable data backups, and tools that simply work — without constant fires, frustration, or downtime. At Crown Computers, we believe IT shouldn’t...

When Is CMMC Compliance Required? What Businesses Must Know to Stay Contract-Eligible
As cyber threats evolve, businesses working with the Department of Defense (DoD) must prioritize CMMC 2.0 compliance to protect sensitive data. The Cybersecurity Maturity Model Certification (CMMC) sets clear requirements for safeguarding Controlled Unclassified...
No Results Found
The page you requested could not be found. Try refining your search, or use the navigation above to locate the post.
Latest news
Reign in your Company’s Email Signatures with CodeTwo
This week we’ll talk about a more overt way that you can make an impact on your customers and vendors: your email signatures…
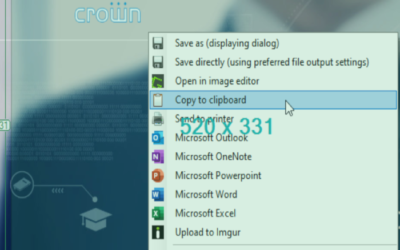
Top 5 Screenshot and Capture Tools
They say a picture is worth a thousand words, and if you’ve been stuck in long work-oriented email chains, you probably know why…
Top 4 Reasons to Encrypt your Email
These days, email gets quite a bit of flack. It’s often insecure and can be messy…
3 Reasons to Secure your Whole Life with MFA
If you use Multi-Factor Authentication (MFA) for your business systems, then you know that it can give you a lot of piece of mind…
Top 5 Things to Consider before Migrating to the Cloud
“The cloud” is now a dominant way of setting up your company’s data and collaborations. At its most basic level…
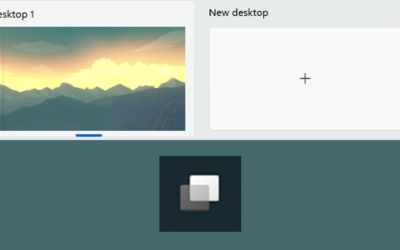
4 Reasons to Start Using the Win+Tab Shortcut
In the past, we’ve covered all of the keyboard shortcuts in Windows, showing you how to use the fastest input method to be the most efficient…
12 Elite Features of Todyl’s Cloud Security Platforms
What Todyl offers is much more than a VPN. Today we will show you 12…
5 Ways to Strengthen On- and Offboarding with IT Solutions
A well-functioning IT department helps you get work done and keeps your data safe…
Protect your Company’s Email with Proofpoint
In today’s cybersecurity landscape, many of the biggest threats to companies find their way into organizations through email….
Understanding the Difference Between Cybersecurity and Network Security Services
With an ever-increasing threat landscape online, businesses have invested in security services to protect themselves against data and network infrastructure threats. Although often confused as synonymous, cybersecurity and network security refer to distinct aspects of...
The Ultimate Cybersecurity Checklist for Small Business Owners
Picture this: You've worked tirelessly to establish your small business, pouring in sweat and tears for years. Your client base is growing exponentially, and your revenue is steadily increasing. But it only takes one cyber-attack to bring it all crashing down. Small...
Protecting Your Email from Hackers: A Guide for Small Business Owners
Despite the popularity of instant messaging, email is still an important part of professional communication. Its ongoing popularity, though, makes it an ideal target for hackers, who are continually finding new methods to steal critical data. As the owner of a small...
Getting The Big Picture: Managing your Network’s Vulnerabilities
Over the past two weeks, we’ve devoted our posts to the recent vulnerability in Microsoft Outlook. It’s been a while since a news story on a vulnerability has hit so hard…
What is Anti Malware and How Does it Work?
Malware is becoming an increasingly serious issue on today's internet. This program infection could result in the loss of personal data, the installation of additional malicious software, or even the destruction of your machine. Malware's effects can range from...
How to Change an Unsecured Wireless Network to Secured
You might be looking to upgrade the security of your home or office wireless network. Trust us, changing it to a secured one is a great initiative for that. An unprotected network can expose you to hackers who can get access to your internet connection and track your...
A New Exploit Makes Two-Factor Auth the Only Option
New exploits are a dime-a-dozen in the software world. There are all sorts of clever things that attackers come up with for stealing your information…
What is IT Security? What You Need to Know
In the digital era, it is crucial to emphasize the significance of IT security. Whether you are an individual or a business, safeguarding sensitive information against cyber threats' perils is pivotal. The question that comes to mind is, what is IT security? In...