Tech News Blog

What Does Cybersecurity Look Like in 2026? Building a Modern Cybersecurity Stack That Actually Protects Your Business
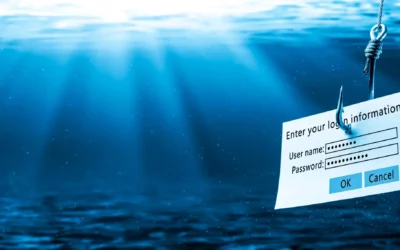
Cyber threats aren’t slowing down—and neither should your defenses. Ransomware, phishing, credential theft, and cloud misconfigurations are now everyday risks for businesses of all sizes. Yet many organizations are still relying on outdated tools or fragmented...

What Does Cybersecurity Look Like in 2026? Building a Modern Cybersecurity Stack That Actually Protects Your Business
Cyber threats aren’t slowing down—and neither should your defenses. Ransomware, phishing, credential theft, and cloud misconfigurations are now everyday risks for businesses of all sizes. Yet many organizations are still relying on outdated tools or fragmented...
No Results Found
The page you requested could not be found. Try refining your search, or use the navigation above to locate the post.
Latest news
How to Protect Your Network from Malware – Tips from the trenchs!
As a business owner who relies on computers or other devices for operations, it's imperative that you learn how to protect your network from malware. Malware, or malicious software, is designed to harm computer systems, steal sensitive data, or cause operational...
What You Need to Know about Apple’s New Rapid Security Response
Basically every week here we find a reason to remind you to do security upgrades, either by installing software updates or hardware/firmware updates on your devices…
Understanding the Benefits of Cloud Computing for Small Businesses
In today's world, small businesses must remain competitive. Small businesses, however, can compete by utilizing cloud computing. Cloud computing technology offers several benefits that can help small businesses cut costs and optimize their operations. Cloud-based...
Understanding the Difference Between Cybersecurity and Network Security Services
With an ever-increasing threat landscape online, businesses have invested in security services to protect themselves against data and network infrastructure threats. Although often confused as synonymous, cybersecurity and network security refer to distinct aspects of...
The Ultimate Cybersecurity Checklist for Small Business Owners
Picture this: You've worked tirelessly to establish your small business, pouring in sweat and tears for years. Your client base is growing exponentially, and your revenue is steadily increasing. But it only takes one cyber-attack to bring it all crashing down. Small...
Protecting Your Email from Hackers: A Guide for Small Business Owners
Despite the popularity of instant messaging, email is still an important part of professional communication. Its ongoing popularity, though, makes it an ideal target for hackers, who are continually finding new methods to steal critical data. As the owner of a small...
Getting The Big Picture: Managing your Network’s Vulnerabilities
Over the past two weeks, we’ve devoted our posts to the recent vulnerability in Microsoft Outlook. It’s been a while since a news story on a vulnerability has hit so hard…
What is Anti Malware and How Does it Work?
Malware is becoming an increasingly serious issue on today's internet. This program infection could result in the loss of personal data, the installation of additional malicious software, or even the destruction of your machine. Malware's effects can range from...
How to Change an Unsecured Wireless Network to Secured
You might be looking to upgrade the security of your home or office wireless network. Trust us, changing it to a secured one is a great initiative for that. An unprotected network can expose you to hackers who can get access to your internet connection and track your...
What Is the Difference between Dedicated and Non Dedicated Server?
Understanding the difference between dedicated and non-dedicated servers is crucial in today's technologically driven world. Knowing which type of server to choose can significantly impact your online experience, whether you're a small business owner or a surfer. So,...
How Can Your Network Be Infected with Malware? 7 Common Ways Malware Can Attack
It's no surprise that, in this era of digital and technological revolution, you may often encounter network security issues that may hamper your business. Files can get missing or encrypted, and passwords no longer working - absolute chaos! In this state, the...
3 More Apps and Marketplaces to Start your AI Era
The newest breakthroughs in “AI” have created a lot of new downstream developments in software. If you look around, everything is becoming AI-driven; in this way, though, it really is just a marketing term that’s replacing the more accurately termed method called...
Why Is IT Security Important: 8 Reasons
You're the proud owner of a thriving business that is growing in leaps and bounds. Your employees are dedicated, your products or services are top-notch, and your customer base continues to expand. But one morning, you wake up to the devastating news that your...
Leverage AI for Better Meetings and Notetaking
A few weeks ago on this blog, we talked about the advantages and limitations of Large Language Model chatbots like ChatGPT. There’s another way that AI tools can help you with your efficiency and streamline your work: taking notes for you in a business meeting. There...
5 Cloud Servers for Small Business: Which Is Better for You?
Being a proud business owner in sunny San Diego, you must feel satisfied seeing your company grow rapidly. With that growth comes the need to store and manage all of your important data efficiently. But here’s the catch – you don’t have the physical space or IT...
What Is a PBX Phone System? Definition, Features, Benefits And Tips
Have you ever wondered what is a PBX phone system and why it's important for businesses? In simple terms, a PBX (Private Branch Exchange) phone system is the backbone of efficient communication within organizations. It acts as your very own private telephone network...
What Is Corporate Data Backup? Everything You Need to Know!
In today's digital age, corporate data is the lifeblood of any organization. From critical business processes to customer information and financial records, a company's valuable data plays a pivotal role in its growth and development. However, as technology advances...