Tech News Blog

A Modern Guide to Managed Service Providers (MSPs) — How to Choose the Right IT Partner for the Future
In today’s always-connected business environment, technology is no longer just a support function — it’s a strategic advantage. Yet for many organizations, managing IT internally has become costly, complex, and risky. That’s where managed service providers (commonly...

How to Fix a Printer: Simple Printer Fixes Businesses Can Try Before Calling Support
Printers always seem to stop working at the worst possible moment — right before a meeting, during payroll runs, or when you're trying to print important client paperwork. If you’re searching for how to fix a printer, you’re definitely not alone. At Crown Computers,...
No Results Found
The page you requested could not be found. Try refining your search, or use the navigation above to locate the post.
Latest news
No Results Found
The page you requested could not be found. Try refining your search, or use the navigation above to locate the post.
Staying One Step Ahead with Mobile Device Security
A lot of us use a mobile device (a phone or tablet) so frequently that we consider it to be our primary computer.
Top 11 Wireless Home Network Security and Usability Tips
WIFI is great for network access. Just be careful who’s accessing your networ…
Get More Value from your Tech with a Technology Business Review
2022 is here, and with the new year, it may be time for new or improved technology solutions for your organization….
Upgrade your Account’s Security by Unlinking Third-Party Apps
When using Google’s or Facebook’s platforms, it may be useful to enable third-party apps or accounts to extend their functionality. However…
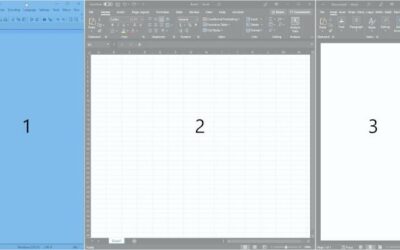
Customize your Windows Desktop Workflow with FancyZones (PowerToys I)
PowerToys is a suite of extensions for Windows that provides a few very powerful features to users who install it…
Avoiding Subnet Conflicts when Using Your Company’s VPN
For more than a year and a half now, remote connections and VPNs have become increasingly important parts of enterprise and personal computing…
Can you Maintain your Privacy around Alexa
(and other Speech Recognition Software)?
Often in the tech world, the more convenient something is then, the less secure or private it is…
Patching Security Holes in Your Software
Patching or updating your software regularly is the one of the strongest ways to protect yourself from…