Tech News Blog

How to Fix a Printer: Simple Printer Fixes Businesses Can Try Before Calling Support
Printers always seem to stop working at the worst possible moment — right before a meeting, during payroll runs, or when you're trying to print important client paperwork. If you’re searching for how to fix a printer, you’re definitely not alone. At Crown Computers,...

What Is a Data Policy? Building Smart Data Governance for Secure, Productive Businesses
Data is the engine that drives today’s organizations — shaping decisions, customer experiences, compliance, and long-term growth. But without clear guidance on how data is collected, stored, protected, and used, that same data can become a serious risk. At Crown...
No Results Found
The page you requested could not be found. Try refining your search, or use the navigation above to locate the post.
Latest news
Cyber Threats, Data Leaks, and Credit: What you Should Know
It’s easy to lose sight of the fact that major corporations face the same challenges, just at a much larger scale…
Reactive Network Defense with Honeypots
Today, we’ll discuss another strategy for securing your networks: the honeypot.
Staying One Step Ahead with Mobile Device Security
A lot of us use a mobile device (a phone or tablet) so frequently that we consider it to be our primary computer.
Top 11 Wireless Home Network Security and Usability Tips
WIFI is great for network access. Just be careful who’s accessing your networ…
Get More Value from your Tech with a Technology Business Review
2022 is here, and with the new year, it may be time for new or improved technology solutions for your organization….
Upgrade your Account’s Security by Unlinking Third-Party Apps
When using Google’s or Facebook’s platforms, it may be useful to enable third-party apps or accounts to extend their functionality. However…
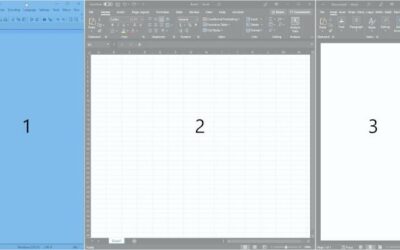
Customize your Windows Desktop Workflow with FancyZones (PowerToys I)
PowerToys is a suite of extensions for Windows that provides a few very powerful features to users who install it…
Avoiding Subnet Conflicts when Using Your Company’s VPN
For more than a year and a half now, remote connections and VPNs have become increasingly important parts of enterprise and personal computing…
Can you Maintain your Privacy around Alexa
(and other Speech Recognition Software)?
Often in the tech world, the more convenient something is then, the less secure or private it is…
Small and Medium Business Cyber Security Checklist
You may tend to think of “security” as one, big thing. In reality, security is many small practices that result in predictability, reliability, and value…
What exactly does “IT Support” mean and Why Your Business Needs It?
When it comes to running a successful business, no matter the size, IT support is an essential component. But, what is “IT support”? In simple terms, IT support offers technical assistance and advice concerning computer systems, hardware, and software. IT support is...
Small Business Network Security: A Comprehensive Guide
Business cybersecurity has become an integral element of any successful company, big or small. With data breaches happening at an alarmingly high rate and cybersecurity threats changing constantly, protecting your small business's networks and data has never been more...
What is Network Security? – Everything You Should Know!
Network security is an essential aspect of any infrastructure. It is the process of using different security measures to protect and secure a network. It helps organizations protect their valuable assets. It prevents cyber attacks, unauthorized access, and other...
Setting Up a Small Business Network: A Step-by-Step Guide
A solid and dependable business car s network is critical for every small firm. Without a well-designed network, businesses will find it difficult to connect, share information, and maintain security measures. A good network helps to produce a smooth workflow with few...
Maximizing Small Business Potential with Cloud Computing: A Comprehensive Guide
Cloud computing is a revolutionary way of managing and storing data on the internet. It allows businesses of any size to access their documents, applications, emails, and other information from any device at any time. Some businesses may want to increase their...
Cybersecurity for Small Business: A Guide to Protecting Your Business Online
Cybersecurity has become an integral component of doing business. Because of small firms' low resources and need for knowledge, they are particularly exposed to cyberattacks. Thus, cybersecurity is no longer a choice for small businesses in today's digital economy; it...
What Is an IT Asset Management? Easiest Way To Understand!
IT asset management (ITAM) is a critical process for organizations of all sizes. It helps make sure that every asset in the inventory used by an organization is available, accurate, and under control. ITAM enables organizations to identify key assets and track...