Tech News Blog

Business Email Compromise: What Every Business Needs to Know to Stay Protected
Business email compromise is one of the fastest-growing and most financially devastating cyber threats facing businesses today. At Crown Computers, we see firsthand how even well-run organizations can fall victim to deceptively simple email-based attacks — often...

What Is ScreenConnect Client and Why Recent Vulnerabilities Have Businesses on High Alert
Remote access tools are a critical part of modern IT operations — but when vulnerabilities surface, they can quickly become a serious business risk. Over the past year, many organizations have been asking urgent questions like “What is ScreenConnect Client?”, “Is...
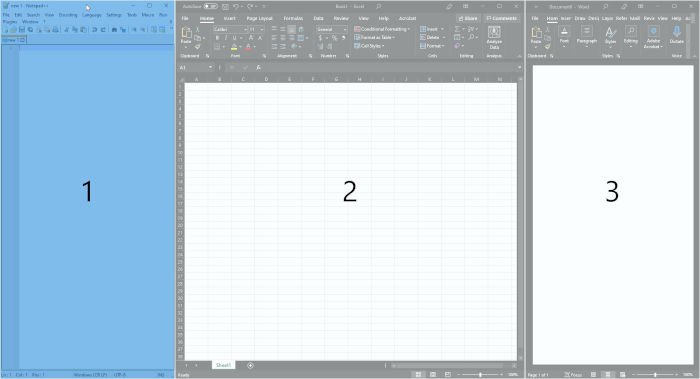
Customize your Windows Desktop Workflow with FancyZones (PowerToys I)
PowerToys is a suite of extensions for Windows that provides a few very powerful features to users who install it…
Latest news
How to Stop Spam Text From Email to Keep Your Email Safe and Spam-Free
Spam can now enter your mobile devices from multiple directions. It could appear as annoying emails, texts, or phone calls. Previously, email was the digital equivalent of postal mail, but now it has your phone numbers. This means that you may also get spam SMS and...
Capture the Flag, but with Ubiquiti Routers and on a Geopolitical Scale
You may have seen some headlines over the past three weeks regarding Ubiquiti routers. Talk of “botnets” and the Department of Justice dismantling Russian malware is pretty splashy. Reading only the headlines, however, won’t give you a sense of the scale of the...
What is IT Support Technician and How do They Work?
IT, or information technology, is a broad field. It includes a variety of jobs, such as engineers, software developers, webmasters, and IT support technicians. The first three examples we just gave could need the help of an IT support technician at some point. But...
How to Use Chat Gpt Effectively For Your Business Tasks?
ChatGPT for Teams is a cost-effective way to boost your team’s documentation and policy skills. As AI continues to grow as a software marketing term, some products really can take your team’s effectiveness to the next level. Copilot and ChatGPT are probably the two...
Ensure Your Security: How to Remove Malware from Network
Malware is a harmful program that infiltrates and damages your devices and networks without your knowledge. They can take various forms, such as legitimate files, hidden codes, and encrypted structures. Regardless of the form, you should definitely know how to remove...
Windows Account Setup Process: Should You Sign in to Your Operating System?
Since Windows 8, Microsoft has been more and more insistent that you sign in to your Microsoft account. But what are the tradeoffs? If you’ve set up a new Windows computer in the last ten years or so, you’ve probably run into a step that asks you to sign in. Over the...
What Is a Secure Email Service? The Ultimate Guide to Choosing the Best Provider
It is common for small businesses to have tight budgets. If a business uses free or cheap web email services, it can save money. However, using such services can turn out to be costly in the long run. A sole data breach can single-handedly destroy a business. That’s...
Catching up on Third-Party Note Taking Apps
As the landscape of automatic recording and transcription matures, are you using the platform that best suits your use case? Now that everyone is getting familiar with AI note taking and transcription, it’s worth taking a look at the features offered by more apps than...
What is a Network Security Policy? A Comprehensive Overview
As the use of networked systems increases, the importance of a solid network security policy becomes increasingly apparent. If businesses do not have a strong policy, they run the danger of serious data breaches and possible damage. A risk-free digital operation is...
Protect Your Devices with a Home Networking Firewall
Numerous harmful programs and hackers are active online, and they want to steal your personal information or get into your computer network system. A home networking firewall keeps those hackers from getting into your home network, just like a security fence does....
The Ultimate Guide to Effective IT Environments Management: Benefits and Challenges
Today’s businesses depend on technology to run their daily tasks and get the most work done. Using technology the right way makes the workplace more efficient. The practice also cuts down on costs and improves communication. However, the way a business manages its IT...
Top 5 Security Threats in Microsoft 365
It's common in the cybersecurity world to note that anything that creates better convenience will also expose users and administrators to more risks. The easier it is to access things, in other words, the less secure those things are. If your organization uses all of...
Demand Management in IT: A Revolutionary Solution in Business Success
A business’s success depends on its ability to guess what customers may want and make sure it has the resources to meet those needs. This is true for IT as well. It is getting harder for IT professionals to provide high-quality services quickly and cheaply while also...
Quickbooks: In the Cloud or On-Prem?
Just a couple of months ago, Intuit announced that they would stop selling many of their Desktop edition software subscriptions at the end of July 2024. While this doesn’t affect existing subscribers (or businesses with QuickBooks Enterprise), it signals to everyone...
Successful IT Management for Small Businesses That Will Boost Productivity
Information Technology (IT) has become significant to almost every aspect of small business operations. Nowadays, smart IT management is of paramount importance for all businesses, no matter how big or small. It is needed to drive digital transformation and lower...
Are “cold emails” ever legitimate?
With all of the emphasis on phishing and social engineering scams, it might be easy to lose sight of old-fashioned swindles. While there are some cutting-edge techniques out there for tricking you into handing over private information (like login/password or payment...
IT Change Management: Navigating The Importance, Types and Best Practices
Businesses constantly have to adjust to new trends in today's fast-paced environment. They go through digital transformation by utilizing technology to take advantage of opportunities and solve problems. However, putting new programs or systems into place isn't always...