Tech News Blog

Humans, AI, and the Future of Cybersecurity: Why Businesses Need Both
Cybersecurity is evolving faster than ever. Artificial intelligence is transforming how threats are detected, analyzed, and responded to—but despite the rise of AI cybersecurity, one truth remains constant: technology alone is not enough. At Crown Computers, we work...

Essential Ways of Workplace IT Management That Boost Productivity & Reduce Downtime
Workplace IT management is the backbone of any modern business. It involves overseeing the essential technology that employees rely on every day, including hardware, software, networks, and user support systems. The goal of effective IT management is not only to...
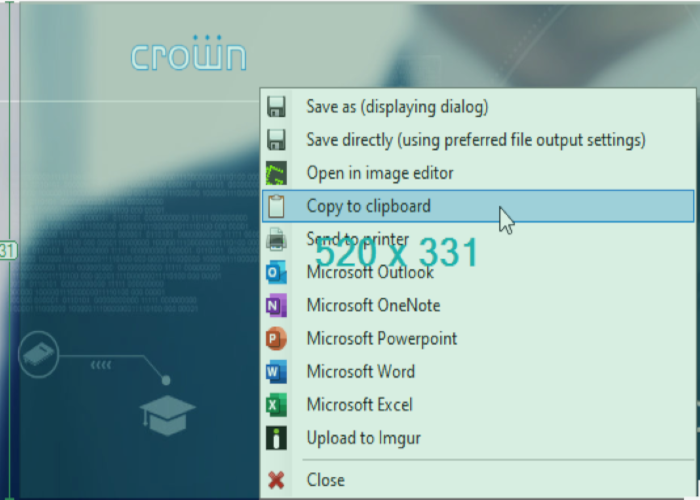
Top 5 Screenshot and Capture Tools
They say a picture is worth a thousand words, and if you’ve been stuck in long work-oriented email chains, you probably know why…
Latest news
Demand Management in IT: A Revolutionary Solution in Business Success
A business’s success depends on its ability to guess what customers may want and make sure it has the resources to meet those needs. This is true for IT as well. It is getting harder for IT professionals to provide high-quality services quickly and cheaply while also...
Quickbooks: In the Cloud or On-Prem?
Just a couple of months ago, Intuit announced that they would stop selling many of their Desktop edition software subscriptions at the end of July 2024. While this doesn’t affect existing subscribers (or businesses with QuickBooks Enterprise), it signals to everyone...
Successful IT Management for Small Businesses That Will Boost Productivity
Information Technology (IT) has become significant to almost every aspect of small business operations. Nowadays, smart IT management is of paramount importance for all businesses, no matter how big or small. It is needed to drive digital transformation and lower...
Are “cold emails” ever legitimate?
With all of the emphasis on phishing and social engineering scams, it might be easy to lose sight of old-fashioned swindles. While there are some cutting-edge techniques out there for tricking you into handing over private information (like login/password or payment...
IT Change Management: Navigating The Importance, Types and Best Practices
Businesses constantly have to adjust to new trends in today's fast-paced environment. They go through digital transformation by utilizing technology to take advantage of opportunities and solve problems. However, putting new programs or systems into place isn't always...
Should Your Organization Voluntarily Comply With Cybersecurity Standards?
As a small- to medium-sized organization, it might be hard to see the benefits of implementing security standards like NIST 800-171, CMMC. or HIPAA (Health Insurance Portability and Accountability). It could seem cumbersome or overkill to align your operations with...
Today’s best ways to call internationally
It’s possible that you’ve noticed that the least important part of your phone is how it serves as a telephone. Now that mobile devices are (rightly) thought of as an ultra-portable computing device, it can be easy to overlook how you’ll stay in touch when traveling...
Bridge the Gap Between Your Mobile Device and Your Computer
Windows Phone Link is the newest way to integrate your phone and your desktop. Choosing which device to use for the most productivity can be fairly simple: writing intensive tasks are usually done more effectively at a device with a physical keyboard while phones have...
How to Check Network for Malware and Tips for Detecting Malware Attacks
The term “malicious network activity” refers to any action that aims to harm, compromise, or abuse a network’s security in any way. If you can’t protect the network from these threats, things can be pretty awful. But before that, you need to check the network to see...
What’s the Difference between Vulnerability Scanning and Penetration Testing?
It's easy to think about network security as an entirely reactive practice. When a new threat arises, typical responses are to install patches or change configurations, or even to upgrade your protection with a new security provider or vendor. There's a lot of...
IT Business Process Management: Definition, Process and Benefits
Inefficiencies and bottlenecks can slow down IT operations. This can hinder a business’s total quality management. IT business process management (BPM) is the solution to these challenges. BPM makes tasks easier and cuts down on mistakes. Teams are able to focus on...
What Is IT Management and Why Is Information Technology Management Important for Businesses?
Businesses today rely significantly on technology to function efficiently. This means an effective IT system that suits the company's needs is essential. So basically, IT management is the foundation of any successful company. It's all about monitoring technological...
Understanding SIEM and Logging in the Modern Stack
As one of the main kinds of security software and services, SIEM (Security Information and Event Management; pronounced either like "seem" or like "sim") can be one of the more straightforward to understand. While it often does involve some advanced AI techniques,...
Top IT Management Frameworks for Businesses
It can be hard for an organization to make sure that its IT (information technology) strategy, processes, and resources all align with its goals and needs. Many different frameworks say they can help with that, but which one is the best? Or is there any direct answer...
Teams vs Teams Premium: Is It Worth Upgrading to Premium Teams?
Your organization might already be using Microsoft Teams for all of your office communications, but you might not have heard of Teams Premium. It's an offering from Microsoft that contains a few serious features for stepping up your company's branding and...
Top 5 Steps to Securing Microsoft 365
In our last blog post, we mentioned some of the biggest security risks to your company's Microsoft 365 suite. It may have seemed like there were a lot of concerns to have over your data's confidentiality and availability-which is right, your data's security is your...
What Is Facilities Management IT: Knowing the Significant Roles and Benefits
Information technology has transformed facility management in the last few decades. In today's fast-paced world, businesses need automated facility management for a sustainable future. This guide will describe the significance of IT in facility management. What Is...
















