Tech News Blog

What Is HBSS? A Complete Guide to Host Based Security Systems for Modern Businesses
In today’s threat landscape, cybersecurity is no longer just about protecting the network perimeter. Every laptop, desktop, and server connected to your environment represents a potential entry point for cybercriminals. That’s why organizations are increasingly asking...

Cloud Assessment Services: Your First Step Toward a Smarter, More Secure Cloud Strategy
Migrating to the cloud can feel overwhelming — but it shouldn’t. With the right strategy, your organization can reduce costs, increase performance, improve security, and unlock new opportunities for growth. At Crown Computers, we help businesses across San Diego and...
No Results Found
The page you requested could not be found. Try refining your search, or use the navigation above to locate the post.
Latest news
Patching Security Holes in Your Software
Patching or updating your software regularly is the one of the strongest ways to protect yourself from…
Employee Security Training is Essential to Your Security
Regular readers of this blog will know that just about every week, the word phishing makes an appearance. It’s just one of many types of attack…
Securing your Devices and Network with Two-Factor and Multi-Factor Authentication
The truth is that passwords still get compromised sometimes, regardless of how strong they are…
How Effective Antivirus Works and Why It Is Important
If it’s been a while since you’ve thought about your antivirus software, you might be relying on a third-party virus scanner or built-in operating system feature…
2 Tips for Using Modern Browsers Securely
The web browser is an important tool for keeping your information secure, but web browsers are changing rapidly…
Could Restarting Your Phone Protect You From Attacks?
More and more, security researchers are finding that malware attacks work less like an app and more like a webpage….
Beware of Tech Support and SEO Scams
Every so often a scam comes along that might take you off guard. I had that experience the other day with a “tech support scam,”
Don’t Wait to Upgrade from Windows Server 2012
The time is coming for Microsoft to end support for Windows Server 2012 and Windows Server 2012 R2. If you’ve already moved on…
9 IT Myths to Move on From This Year
It’s easy to have some misconceptions about business technology since it moves quickly and is very complex. You could…
Watch Out for HTML in Emails!
With the new year here, it might be time to not just look forward, but take stock of something that comes up a lot on the blog: email safety…
3 Security Services to Consider in 2023
If you’ve had a good year security-wise, you may not be thinking about how to enhance your company’s defenses against malware and scams…
Reign in your Company’s Email Signatures with CodeTwo
This week we’ll talk about a more overt way that you can make an impact on your customers and vendors: your email signatures…
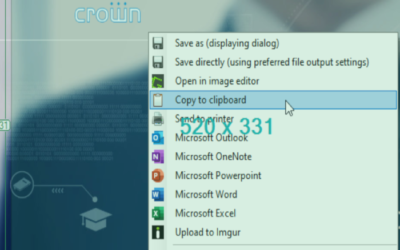
Top 5 Screenshot and Capture Tools
They say a picture is worth a thousand words, and if you’ve been stuck in long work-oriented email chains, you probably know why…
Top 4 Reasons to Encrypt your Email
These days, email gets quite a bit of flack. It’s often insecure and can be messy…