Tech News Blog

Cloud Assessment Services: Your First Step Toward a Smarter, More Secure Cloud Strategy
Migrating to the cloud can feel overwhelming — but it shouldn’t. With the right strategy, your organization can reduce costs, increase performance, improve security, and unlock new opportunities for growth. At Crown Computers, we help businesses across San Diego and...

Cloud Assessment Services: Your First Step Toward a Smarter, More Secure Cloud Strategy
Migrating to the cloud can feel overwhelming — but it shouldn’t. With the right strategy, your organization can reduce costs, increase performance, improve security, and unlock new opportunities for growth. At Crown Computers, we help businesses across San Diego and...
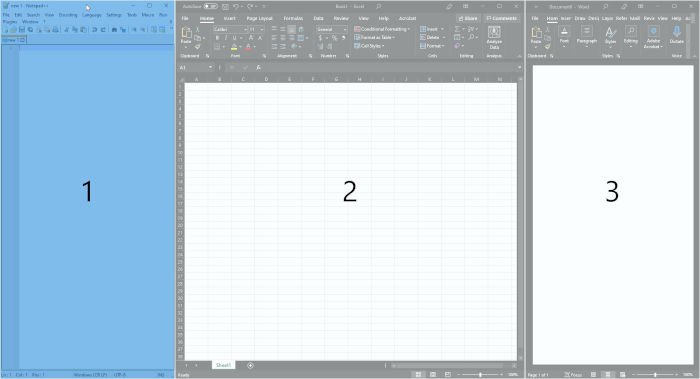
Customize your Windows Desktop Workflow with FancyZones (PowerToys I)
PowerToys is a suite of extensions for Windows that provides a few very powerful features to users who install it…
Latest news
How to Use Chat Gpt Effectively For Your Business Tasks?
ChatGPT for Teams is a cost-effective way to boost your team’s documentation and policy skills. As AI continues to grow as a software marketing term, some products really can take your team’s effectiveness to the next level. Copilot and ChatGPT are probably the two...
Ensure Your Security: How to Remove Malware from Network
Malware is a harmful program that infiltrates and damages your devices and networks without your knowledge. They can take various forms, such as legitimate files, hidden codes, and encrypted structures. Regardless of the form, you should definitely know how to remove...
Windows Account Setup Process: Should You Sign in to Your Operating System?
Since Windows 8, Microsoft has been more and more insistent that you sign in to your Microsoft account. But what are the tradeoffs? If you’ve set up a new Windows computer in the last ten years or so, you’ve probably run into a step that asks you to sign in. Over the...
What Is a Secure Email Service? The Ultimate Guide to Choosing the Best Provider
It is common for small businesses to have tight budgets. If a business uses free or cheap web email services, it can save money. However, using such services can turn out to be costly in the long run. A sole data breach can single-handedly destroy a business. That’s...
Catching up on Third-Party Note Taking Apps
As the landscape of automatic recording and transcription matures, are you using the platform that best suits your use case? Now that everyone is getting familiar with AI note taking and transcription, it’s worth taking a look at the features offered by more apps than...
What is a Network Security Policy? A Comprehensive Overview
As the use of networked systems increases, the importance of a solid network security policy becomes increasingly apparent. If businesses do not have a strong policy, they run the danger of serious data breaches and possible damage. A risk-free digital operation is...
Get The Most Out of Your Windows Operating System With PowerToys
PowerToys has been a perennial favorite here at Crown Computers. As a suite of extended functions made by Microsoft to integrate with Windows, it’s kind of a shame that it’s a separate program that needs to be installed and updated on its own. While these features...
Small Business Network Design: Empowering Growth and Collaboration
The computer network setup is at the heart of every small business. As the internet is becoming the most important business communication tool, making a small business network design based on the internet and computers is very important and should be done right away....
Scams or Service: Avoid Malicious Google Ads
If you find yourself needing information on a product, a service, or customer support, you probably instinctively reach for Google. While Google might be a convenient way to get information for a lot of things, customer support should probably be taken off the list....
Quickbooks: In the Cloud or On-Prem?
Just a couple of months ago, Intuit announced that they would stop selling many of their Desktop edition software subscriptions at the end of July 2024. While this doesn’t affect existing subscribers (or businesses with QuickBooks Enterprise), it signals to everyone...
Successful IT Management for Small Businesses That Will Boost Productivity
Information Technology (IT) has become significant to almost every aspect of small business operations. Nowadays, smart IT management is of paramount importance for all businesses, no matter how big or small. It is needed to drive digital transformation and lower...
Are “cold emails” ever legitimate?
With all of the emphasis on phishing and social engineering scams, it might be easy to lose sight of old-fashioned swindles. While there are some cutting-edge techniques out there for tricking you into handing over private information (like login/password or payment...
IT Change Management: Navigating The Importance, Types and Best Practices
Businesses constantly have to adjust to new trends in today's fast-paced environment. They go through digital transformation by utilizing technology to take advantage of opportunities and solve problems. However, putting new programs or systems into place isn't always...
Should Your Organization Voluntarily Comply With Cybersecurity Standards?
As a small- to medium-sized organization, it might be hard to see the benefits of implementing security standards like NIST 800-171, CMMC. or HIPAA (Health Insurance Portability and Accountability). It could seem cumbersome or overkill to align your operations with...
Today’s best ways to call internationally
It’s possible that you’ve noticed that the least important part of your phone is how it serves as a telephone. Now that mobile devices are (rightly) thought of as an ultra-portable computing device, it can be easy to overlook how you’ll stay in touch when traveling...
Bridge the Gap Between Your Mobile Device and Your Computer
Windows Phone Link is the newest way to integrate your phone and your desktop. Choosing which device to use for the most productivity can be fairly simple: writing intensive tasks are usually done more effectively at a device with a physical keyboard while phones have...
How to Check Network for Malware and Tips for Detecting Malware Attacks
The term “malicious network activity” refers to any action that aims to harm, compromise, or abuse a network’s security in any way. If you can’t protect the network from these threats, things can be pretty awful. But before that, you need to check the network to see...