Introduction
Common cyberthreats like phishing emails can have catastrophic effects, including identity theft, financial loss, and stolen data. These emails frequently trick users into submitting sensitive information like passwords, credit card numbers, and other personal details by appearing authentic. To protect yourself and your data, it is vital to understand how to detect phishing emails.
We’ll provide you with seven useful tips in this post on how to spot and stay away from phishing emails. In the modern digital world, where phishing assaults are getting more complex and common, these guidelines will help you stay safe and secure.
Definition of Phishing
Phishing is a type of cyber attack that involves sending fraudulent emails, texts, or other communications to trick individuals into providing sensitive information. These scams often impersonate legitimate organizations, such as banks or social media platforms, and can result in identity theft or financial loss.
According to the FBI’s Internet Crime Complaint Center, phishing was the third most common cybercrime in 2020, with 241,342 reported incidents. The Anti-Phishing Working Group reported that there were 139,685 unique phishing websites detected in the first quarter of 2021.
Some common examples of phishing include emails that appear to be from a bank, requesting account information or login credentials, or emails from social media platforms requesting users to verify their accounts. It’s essential to remain vigilant and cautious when receiving any unsolicited emails or communications requesting personal information.
Why is it important to detect phishing emails?
Phishing emails could lead to identity theft, financial loss, and data breaches; therefore, spotting them is vital. According to an IBM estimate, the average cost of a data breach in 2020 was $3.86 million. The complexity of phishing schemes is rising, and it’s easy to fall for them.
For instance, a phishing email posing as one from a well-known online store may ask the customer to confirm their account details. The email can include a link that takes the recipient to a phony website created to steal personal data.
Individuals can protect themselves and their sensitive information from thieves by recognizing and avoiding phishing emails. Continuous surveillance and a commitment to best practices can aid in mitigating risk and preserving the security of personal information.
How to Detect Phishing Emails: 8 Ways to Detect
Now you need to know how to identify fraudulent emails. Here are seven practical ways to detect phishing emails and protect your data from cybercriminals.
1. Check the sender’s email address for signs of fraudulence
Examining the sender’s email address for fraudulence is one of the simplest methods to spot phishing emails. To make people believe they are coming from a reliable source, cybercriminals frequently use phony or similar-sounding email addresses- an email from “Paypa1.com” rather than “Paypal.com,” for instance.
It’s important to thoroughly review the sender’s email address and search for any unusual or ominous information. By doing this, you may protect your data from phishing attacks and prevent becoming a victim.
2. Watch for misspellings and grammar mistakes
Another way to detect phishing emails is to watch for misspellings and grammar mistakes. Cybercriminals often use automated translation tools to create phishing emails, resulting in errors that can be dead giveaways. For example, an email from a supposed “bank” that says, “your account is at risk. “Please provide account information” could be a phishing attempt. Paying close attention to the language used in the email and looking for inconsistencies can help you avoid falling victim to these scams.
3. Don’t click on links in suspicious emails
One crucial tip for detecting phishing emails is to avoid clicking on any links within suspicious emails. Cybercriminals often use these links to direct individuals to fake websites that look like legitimate ones, tricking them into giving away personal information. Instead of clicking on the link, it’s safer to go directly to the website and check your account status.
4. Be careful with attachments
Another tip for detecting phishing emails is to be cautious with attachments. Cybercriminals may attach malicious software to an email disguised as a legitimate document. Do not access a file if you did not request it or doubt its legitimacy. A phishing effort could look like an email from a coworker with a file called “Invoice.pdf,” for instance. Before accessing any files, it’s crucial to double-check with the alleged sender.
5. Don’t fall for urgency or threats
In order to get their target to act right away, phishing emails frequently attempt to instill fear or a sense of urgency. Cybercriminals frequently employ this technique to deceive people into clicking on links or downloading files that could jeopardize their confidential information. It’s critical to maintain composure and evaluate the situation before acting. Beware of emails that offer rewards that seem too good to be true or threaten dire consequences if you don’t respond immediately.
6. Protect your personal information
Another essential tip for detecting phishing emails is to protect your personal information. Phishers often try to trick you into providing personal information, such as your social security number or credit card details, which they can use to steal your identity or money. Be careful with emails that ask for this kind of sensitive information, and call the company to make sure the request is real. Remember, legitimate companies will never ask you to provide personal information via email.
7. Trust your instincts
One of the best ways to detect a phishing email is to trust your instincts. If an email appears to be too good to be true, it most likely is. It’s worth double-checking if the sender appears suspicious or if the message seems out of character for them. Always err on the side of caution, and if you’re unsure whether an email is legitimate, don’t be afraid to ask someone else. Don’t forget that it is better to be safe than sorry. Phishers frequently use psychological tactics to persuade you to act fast, so take a step back, think it over, and trust your instincts.
8. Watch out for Tricky graphics
This is one of the trickiest ways bad actress will try to get unsuspected humans to click on something is with a picture that looks something like this.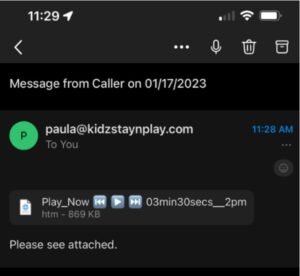
What to Do if You Receive a Phishing Email
Receiving a phishing email can be unsettling, but it’s important to know how to respond. Here are two cents on this:
Don’t reply, click on links or download attachments
Firstly, don’t reply, click on any links, or download any attachments. Doing so may compromise your security and give the phisher access to your personal information. Secondly, report the email to your IT department or relevant authorities. By reporting the phishing email, you can help prevent others from falling victim to the same scam. Your IT department can investigate the email and take steps to protect your organization from future attacks.
Report the email to your IT department or relevant authorities
Reporting the phishing email to the relevant authorities can aid in their efforts to track down and prosecute the perpetrators. Remember, taking immediate action plays a big part in minimizing the impact of a phishing attack. So don’t hesitate to take the necessary steps to protect yourself and your organization.
Delete the email from your inbox and trash folders
Once you’ve identified a phishing email, don’t let it fester in your inbox like expired leftovers in the fridge. Hit that delete button and permanently remove it from both your inbox and trash folders.
By doing so, you reduce the risk of accidentally interacting with the malicious content again. It’s just like disposing of hazardous waste—keeping yourself safe from potential harm!
Monitor your accounts for any suspicious activity
After encountering a suspected phishing email, it’s essential to be proactive and monitor your accounts for any signs of unusual activity. Keep an eye out for unauthorized transactions, unfamiliar logins, or any changes to your personal information.
Remember that cybercriminals may attempt to gain access to your sensitive data, so staying vigilant is key. If you notice anything suspicious, notify your bank or relevant service provider immediately and take the necessary steps to protect yourself from potential harm.
How to Protect Yourself from Phishing Attacks
Phishing attacks are becoming more prevalent, and you may suffer to a severe extent due to this. Fortunately, there are precautions you can take to safeguard yourself and your business.
Educate yourself and your employees about phishing attacks
First and foremost, don’t undermine the value of education. It is critical to remain up to date on the newest phishing tactics and to educate your workers on how to identify and prevent them. This includes the ability to recognize fraudulent communications and know what to do if they receive one.
Use anti-phishing software
Using anti-phishing tools can also help you safeguard yourself. These applications can assist in detecting and preventing phishing efforts before they reach your inbox.
Keep your software up to date
It is also essential to keep your software current. Many phishing attacks depend on leveraging weaknesses in outdated software, so keeping your operating system, web browser, and other software up to date can help you avoid these attacks.
Use strong passwords and two-factor authentication
Protecting yourself from phishing attacks is easier if you use two-factor authentication and secure passwords. Passwords that use a mix of letters, digits, and special characters are the most secure. By demanding a second form of verification, such as a fingerprint or a number sent to your phone, two-factor authentication adds an additional layer of protection.
Be careful what you share online
You must exercise caution when sharing information online. Phishing attacks frequently depend on social engineering, which means that attackers may create persuasive phishing emails using personal information obtained from social media accounts.
How Can Crown Computers Help You?
Crown Computers knows how important it is for computer networks to be safe in this era. As online risks get more complicated and widespread, it’s more important than ever to have strong defenses in place. You will receive a wide range of network security services from us to make sure that your information is kept private and safe.
Our team of knowledgeable experts will collaborate with you to identify your specific security requirements in order to prevent cyberattacks on your network. We can handle all your security needs, from antivirus and anti-malware tools to firewalls and attack defense systems. You can have faith that Crown Computers will keep your network safe. Contact us right away if you want to learn more about the services we provide.
Conclusion
In the end, all we have to say is, staying safe from phishing attacks requires vigilance and a proactive approach. By following the tips and strategies outlined in this guide, you can reduce the risk of falling victim to these scams. Working with a reputable computer security company like Crown Computers can provide added protection and peace of mind. Remember to always stay alert and take steps to protect your personal and business information from cyber threats.
